Fingerprint Public Key . These are github's public key fingerprints:. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. public key fingerprints can be used to validate a connection to a remote server. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting.
from askleo.com
By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. public key fingerprints can be used to validate a connection to a remote server. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. These are github's public key fingerprints:. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting.
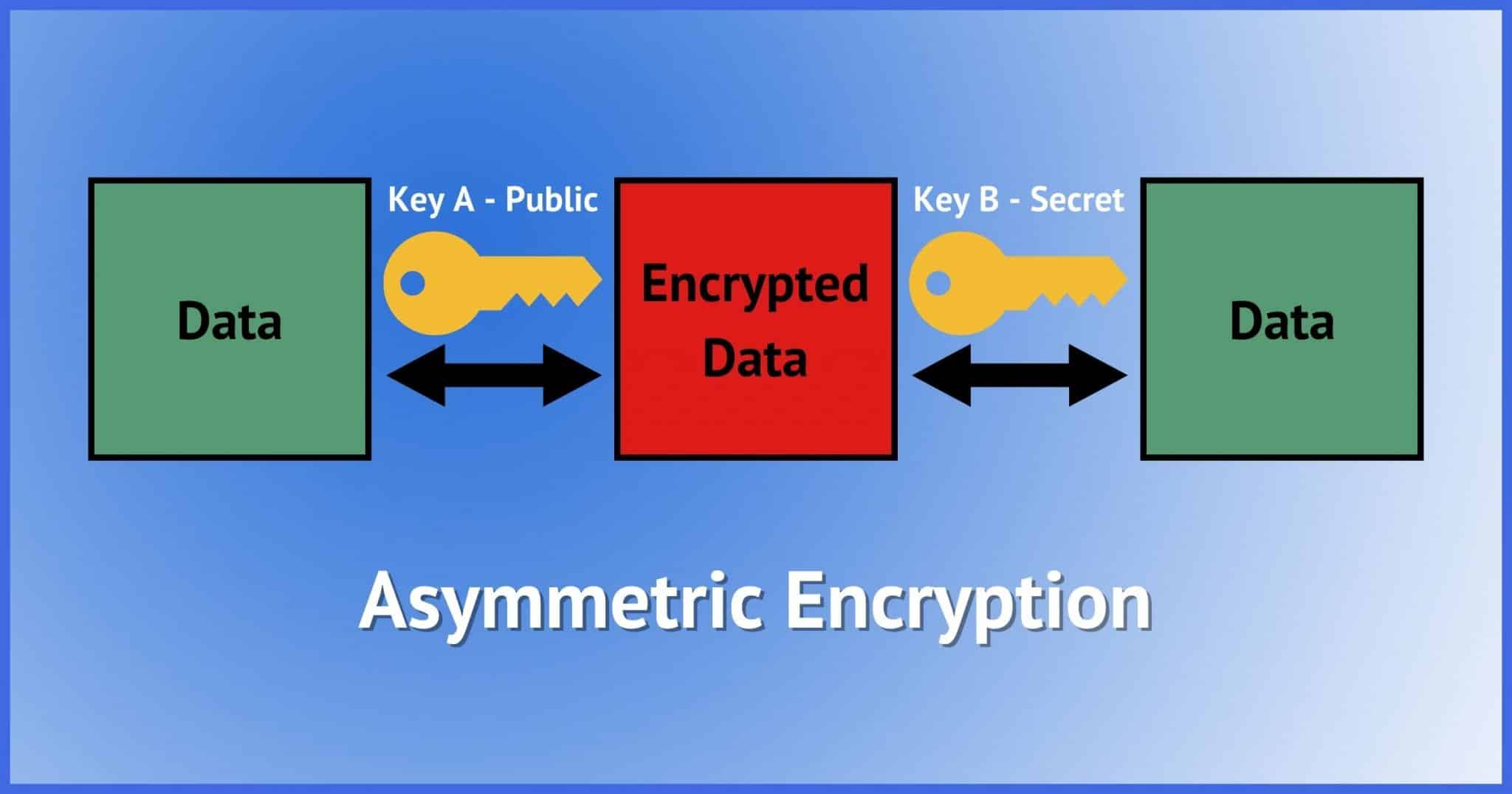
What Is Public Key Cryptography? Ask Leo!
Fingerprint Public Key generating a strong ssh key pair is crucial for ensuring the security of your remote connections. public key fingerprints can be used to validate a connection to a remote server. These are github's public key fingerprints:. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. generating a strong ssh key pair is crucial for ensuring the security of your remote connections.
From madisonsheriff.com
Fingerprinting Madison County Sheriff's Office Fingerprint Public Key public key fingerprints can be used to validate a connection to a remote server. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. the ssh/sftp key fingerprint. Fingerprint Public Key.
From www.hermiston.or.us
Fingerprinting Hermiston, OR Fingerprint Public Key These are github's public key fingerprints:. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. generating a strong ssh key pair is crucial for ensuring the security of your. Fingerprint Public Key.
From stackoverflow.com
ssh public key fingerprint does not match. Maninthemiddle attack Fingerprint Public Key the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. These are github's public key fingerprints:. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with. Fingerprint Public Key.
From thetis.io
Thetis FIDO2 Fingerprint Security Key Fingerprint Public Key public key fingerprints can be used to validate a connection to a remote server. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. the ssh/sftp key fingerprint aids in server authentication by allowing client. Fingerprint Public Key.
From attorneyatlawmagazine.com
3 Major Types of Fingerprints Find Out the Various Types of Fingerprint Public Key the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. These are github's public. Fingerprint Public Key.
From de-academic.com
Public Key Fingerprint Fingerprint Public Key public key fingerprints can be used to validate a connection to a remote server. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which. Fingerprint Public Key.
From www.christiancountyso.com
Fingerprinting Christian County Sheriff's Department Fingerprint Public Key public key fingerprints can be used to validate a connection to a remote server. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. These are github's public key fingerprints:. By generating an ssh key pair and extracting its fingerprint (s), you can securely. Fingerprint Public Key.
From sites.rutgers.edu
Fingerprinting and Science Today Fingerprinting in the Modern World Fingerprint Public Key the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. public key fingerprints can be used to validate a connection to a remote server. These are github's public. Fingerprint Public Key.
From www.scribd.com
Deanonymizing Tor Network Communications Using Deep Learning Fingerprint Public Key These are github's public key fingerprints:. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. generating a strong ssh key pair is crucial for ensuring the security. Fingerprint Public Key.
From wellesleyps.org
Fingerprinting Requirements Human Resources Fingerprint Public Key By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. These are github's public key fingerprints:. the fingerprint is based on the host's public key, usually based on the. Fingerprint Public Key.
From cyberhoot.com
Fingerprint CyberHoot Cyber Library Fingerprint Public Key public key fingerprints can be used to validate a connection to a remote server. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. These are github's public. Fingerprint Public Key.
From www.ci.mequon.wi.us
Public Fingerprinting Mequon Wisconsin Fingerprint Public Key the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. These are. Fingerprint Public Key.
From thetis.io
Thetis FIDO2 Fingerprint Security Key Fingerprint Public Key These are github's public key fingerprints:. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. public key fingerprints can be used to validate a connection to a remote. Fingerprint Public Key.
From techhyme.com
Public Key Cryptography A Brief Guide Tech Hyme Fingerprint Public Key the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. generating a strong ssh key pair is crucial for ensuring the security of your remote connections. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted. Fingerprint Public Key.
From ssd.eff.org
A Deep Dive on EndtoEnd Encryption How Do Public Key Encryption Fingerprint Public Key By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. These are github's public key fingerprints:. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. generating a strong ssh key pair is crucial for ensuring the security of your. Fingerprint Public Key.
From www.ledger.com
What Are Public Keys and Private Keys? Ledger Fingerprint Public Key These are github's public key fingerprints:. public key fingerprints can be used to validate a connection to a remote server. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. By generating an ssh key pair and extracting its fingerprint (s), you can securely. Fingerprint Public Key.
From thetis.io
Thetis FIDO2 Fingerprint Security Key Fingerprint Public Key These are github's public key fingerprints:. By generating an ssh key pair and extracting its fingerprint (s), you can securely authenticate and establish encrypted communication channels with remote systems. public key fingerprints can be used to validate a connection to a remote server. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the. Fingerprint Public Key.
From askleo.com
What Is Public Key Cryptography? Ask Leo! Fingerprint Public Key public key fingerprints can be used to validate a connection to a remote server. the fingerprint is based on the host's public key, usually based on the /etc/ssh/ssh_host_rsa_key.pub file. the ssh/sftp key fingerprint aids in server authentication by allowing client applications to verify the identity of the server to which they are connecting. These are github's public. Fingerprint Public Key.